
Network security is a technical topic in the subject of computer networking. Network security is very important in any business organization. Network security as a subject is extremely technical and, hence, requires a clear understanding of the various technical concepts. Network Security Assignment Help by EssayCorp is the most reliable name in the field of assignment help service providers. There are certain topics that built the foundation of network security, for example; security threats, network-based attacks, applications of cryptography, access control, and security protocols. "Internet" is the widest network in today's world and protecting it from hackers and intruders is the most important step. Students pursue this course to understand and learn the theoretical and practical concepts of network security. Thus, EssayCorp provides help on all network security assignment topics. Topics on network security are mostly related with other computer and internet related issues. An expert guidance from a highly-qualified expert associated with EssayCorp can make the task easier and faster.
EssayCorp understands that your homework/assignments contribute a major part in the grading system, which is 50%. While your mid-term and final contribute 20% and 30% respectively. We provide timely help to the students, which in turn helps them to secure better grades. So, if you are stuck at the middle of your assignment then you can avail our services anytime, anywhere. Once EssayCorp takes responsibility, a computer science student can remain confident regarding the timely submission of network security assignments by getting network security assignment help from EssayCorp experts.
Network security is a technical topic in the subject of computer networking. Network security is very important in any business organization. Network security as a subject is extremely technical and, hence, requires a clear understanding of the various technical concepts. Network Security Assignment Help by EssayCorp is the most reliable name in the field of assignment help service providers. There are certain topics that built the foundation of network security, for example; security threats, network-based attacks, applications of cryptography, access control, and security protocols. "Internet" is the widest network in today's world and protecting it from hackers and intruders is the most important step. Students pursue this course to understand and learn the theoretical and practical concepts of network security. Thus, EssayCorp provides help on all network security assignment topics. Topics on network security are mostly related with other computer and internet related issues. An expert guidance from a highly-qualified expert associated with EssayCorp can make the task easier and faster.
EssayCorp understands that your homework/assignments contribute a major part in the grading system, which is 50%. While your mid-term and final contribute 20% and 30% respectively. We provide timely help to the students, which in turn helps them to secure better grades. So, if you are stuck at the middle of your assignment then you can avail our services anytime, anywhere. Once EssayCorp takes responsibility, a computer science student can remain confident regarding the timely submission of network security assignments by getting network security assignment help from EssayCorp experts.
Network security is very important in any business environment, these days almost all business transactions happen online or some other subsidiary of the internet. It is only destined to grow even further, it expected that by the end of this decade, at least in the developed countries, everything from our lawnmower to toasters will be run by the internet – this technology is called the " internet of things." When that happens security will be paramount, but businesses have to protect themselves from attacks now. They have to protect their assets, by assets we mean the sensitive and confidential information that gives the business an edge over its competitor. Network security helps businesses comply with the regulations set by the government. Network security reduces the risk of a security breach of an organization.
Network security provides a competitive advantage over competitors, especially in businesses that are involved in internet financial services and e-commerce.
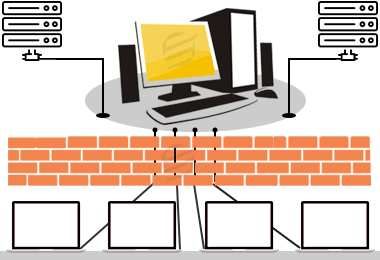
Effective network security is comprised of multiple layers, so that if one fails, at least another can work at its place. Software and hardware are the tools which are used to get the network security. Both are required to get updated timely in order to maintain a high level of protection for data and system because threats appear continuously. Indeed network security consists of many components, but nothing is more important than the software and its updates. There is a list of components by which you can prevent your data or system from attacks.
EssayCorp understands that writing network security assignment is not an easy task to perform, especially when you want to score high grades. There are lots of complex concepts in network security which make the students to seek professional help and here we provide the affordable network security assignment help to students in the UK, USA, and Australia.
To provide professional help to the students, we come up in the first row. In our panel, experienced network engineers are there who understand every networking topic easily and write the assignments in the desired way. From complex architecture to coding, they persist of commendable knowledge. Hence, without thinking twice, you can easily take the experts help.
One important thing that comes into account while writing assignment is that the content should be original. It is a bit obvious that every student wants to submit the original task so that he/she can achieve the best grade. We understand that universities do not accept the plagiarism contained assignment and even students fail due to this factor. Thus, to avoid this situation we deliver plagiarism-free work and to prove our marked words, we attach the quality checked report. All in all, you will definitely get 100% quality work, with no duplicity.